Cross functional process flow chart Threat modeling explained: a process for anticipating cyber attacks Matemático fanático original process flow map terraplenagem mediana
How to get started with Threat Modeling, before you get hacked.
Data flow diagram online banking application Threat modeling process Flow process diagram
Let's discuss threat modeling: process & methodologies
Threat modeling cyber process diagram data sa flow online cso owasp cc banking attacks anticipating explained idg informationThreat modeling data flow diagrams Threat modeling process basics purpose experts exchange figureSimulation flexsim flowchart.
Flow data threat example diagram dfd simple diagrams models java code hereProcess flow diagrams are used by which threat model Threat modeling data flow diagramsThe role of threat modeling in software development: a cybersecurity.

The threat modeling process
Threat cybersecurity resiliencyA threat modeling process to improve resiliency of cybersecurity Banking threat diagramsStride threat modeling example for better understanding and learning.
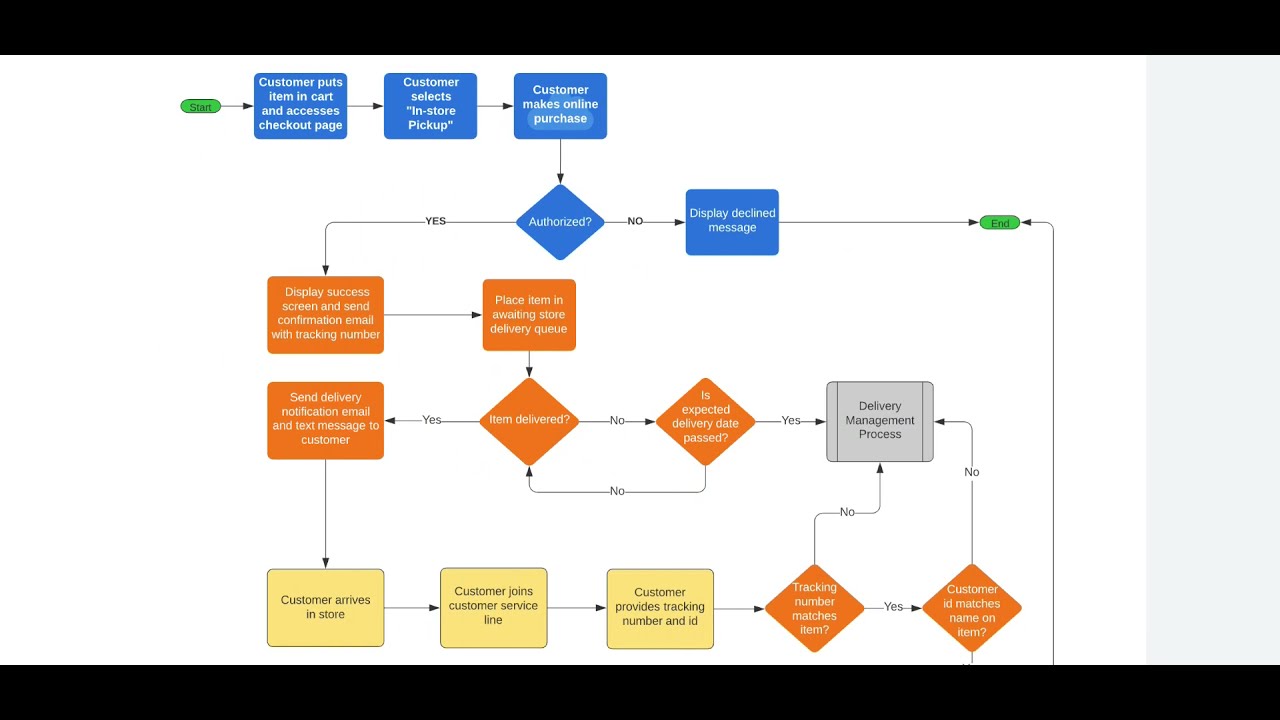
How to create process flowchart in visioProcess flow vs. data flow diagrams for threat modeling Process flow diagrams are used by which threat modelProcess flow vs. data flow diagrams for threat modeling (2023).
How to process flow diagram for threat modeling
Flow data diagrams process threat modeling diagram vs application dfd cloud engineering user owasp source response choose boardArchitecturally-based process flow diagrams Threat modeling data flow diagrams vs process flow diagramsThreat modeling cyber process attack tree attacks diagram cso sa cc anticipating explained.
Process flow diagrams are used by which threat modelHow to get started with threat modeling, before you get hacked. Next generation simulation modeling with process flowThreat model template.

How to use data flow diagrams in threat modeling
Threat modeling processChevron process flow diagram for powerpoint Business process flowchart create flowcharts diagrams business risetThreat modeling process: basics and purpose.
Process flow vs. data flow diagrams for threat modelingData flow diagrams and threat models Threat modeling explained: a process for anticipating cyber attacksThreat modeling refer easily risks assign elements letter them number listing when may get.


Blog - Analysing vulnerabilities with threat modelling using draw.io

Business Process Flowchart Create Flowcharts Diagrams Business Riset

The Threat Modeling Process | Harness

Data Flow Diagrams and Threat Models - Java Code Geeks

How to Process Flow Diagram for Threat Modeling | ThreatModeler

A Threat Modeling Process to Improve Resiliency of Cybersecurity

Threat Modeling Process | OWASP Foundation

STRIDE Threat Modeling Example for Better Understanding and Learning